











Industrial systems operate under strict constraints—segmented networks, limited connectivity, and tightly controlled access. Without the right security model, data movement introduces risk and operations become harder to govern.
Industrial environments require more than basic cybersecurity. Data Security creates a controlled, resilient foundation so data can move safely across systems and sites without disrupting production.
Data Security spans every layer of the industrial data foundation and ensures industrial systems can operate with confidence. By protecting systems, controlling access, and securing data movement, it creates the conditions required to scale data operations, analytics, and Industrial AI—without introducing risk or disrupting production.
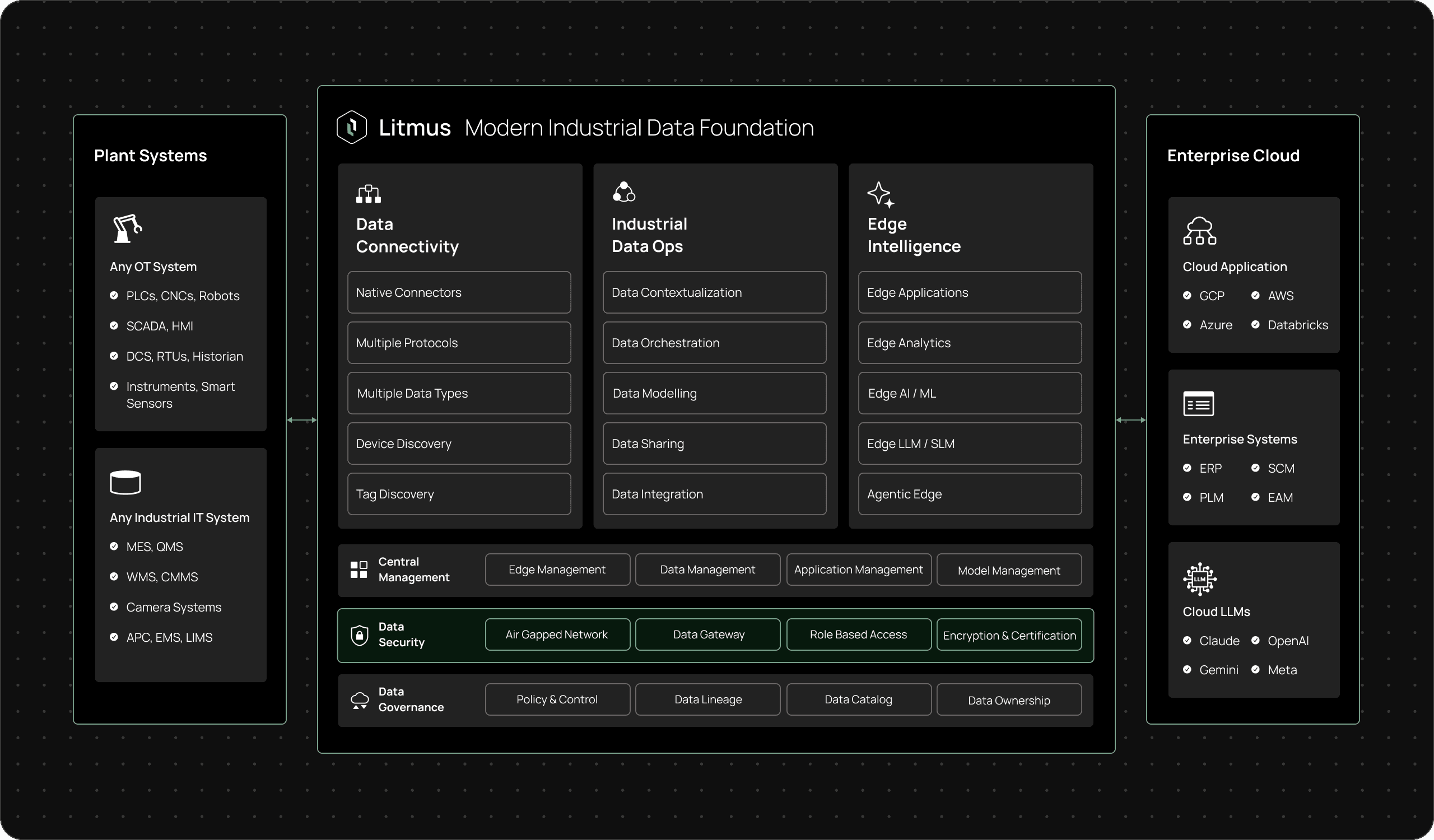
standardized industrial data architecture

optimized packing and volume tracking

standardized industrial data architecture
Real-time monitoring and corrective action

Protect systems, control access, and secure data movement so industrial operations remain resilient across environments.
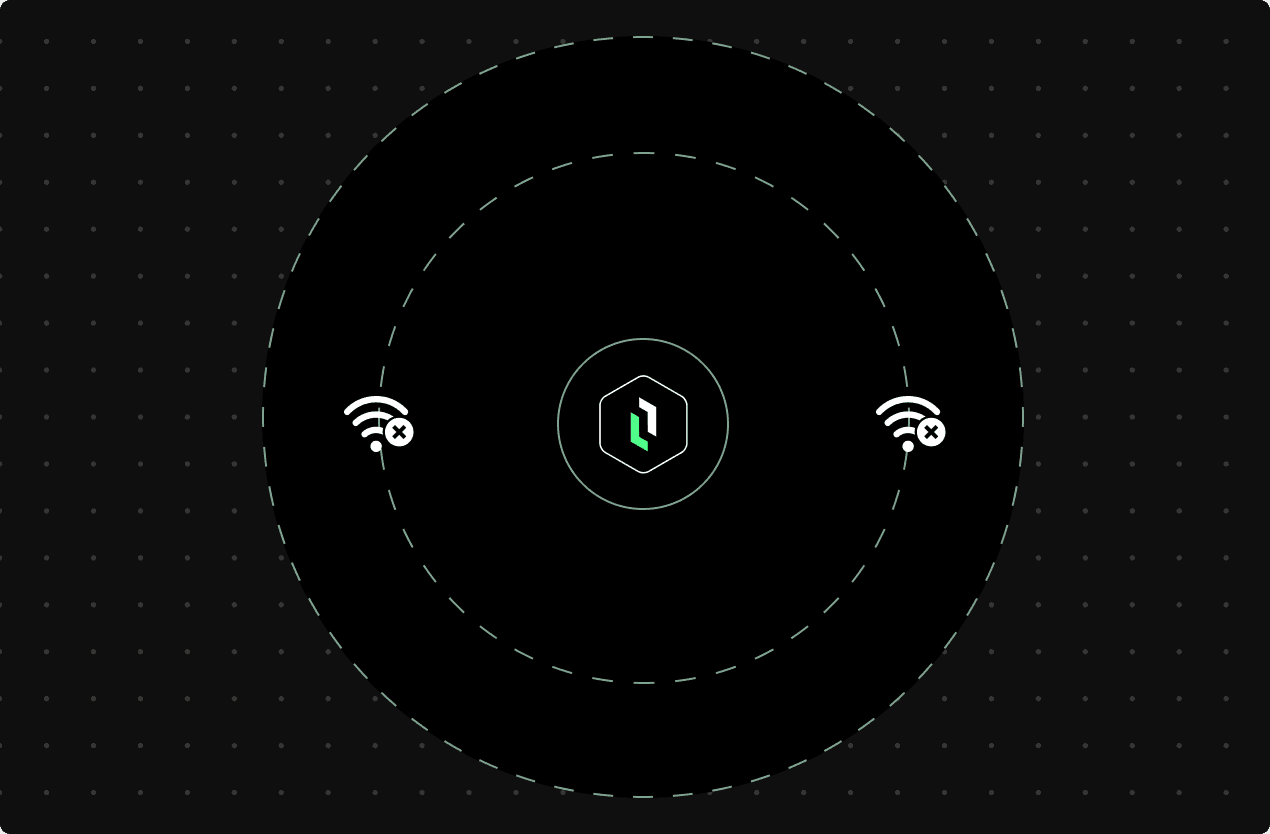
AIR-gapped network
Many industrial environments require isolated execution models where external connectivity is limited or restricted. Data Security enables secure operation in these environments without disrupting local workflows.
What this enables:
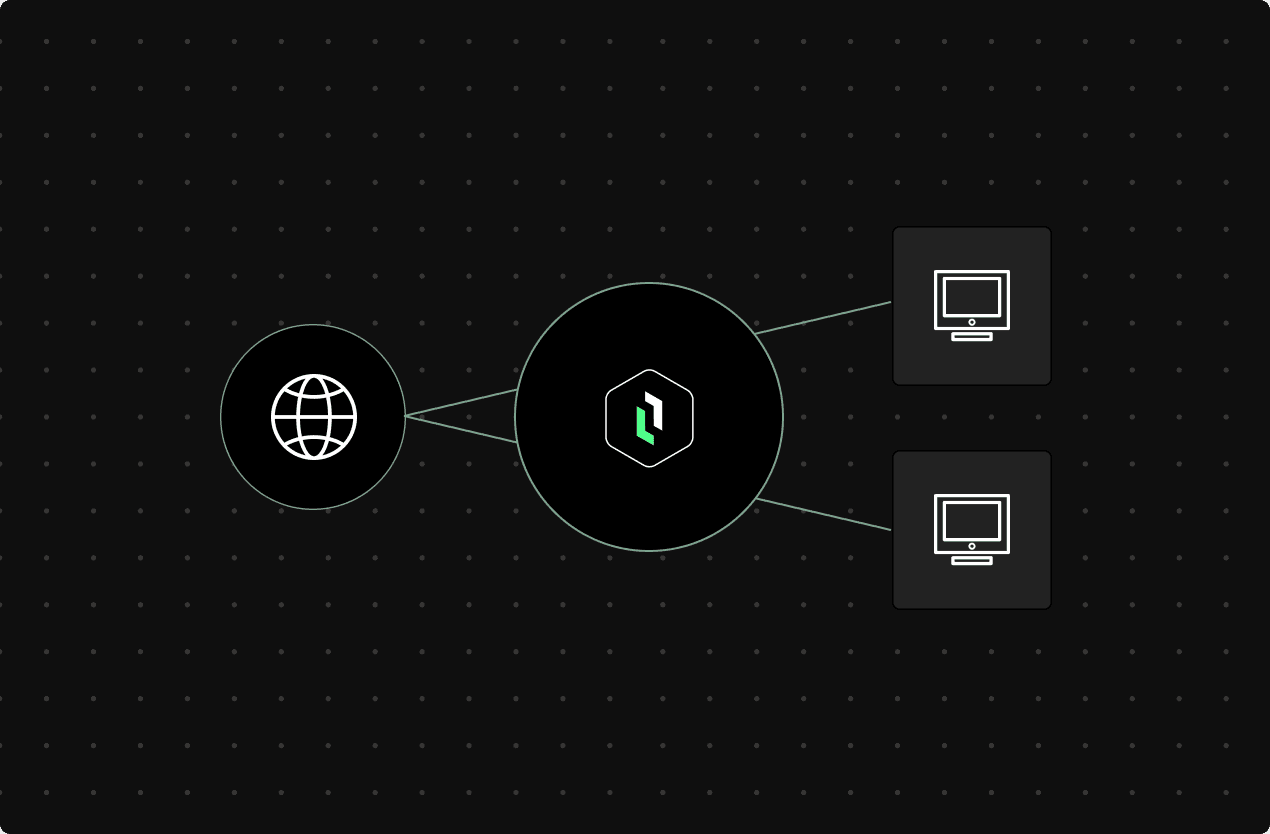
Data Gateway
Industrial data movement must be controlled and policy-driven. A data gateway ensures that only approved data leaves production environments while maintaining reliability across network boundaries.
What this enables:
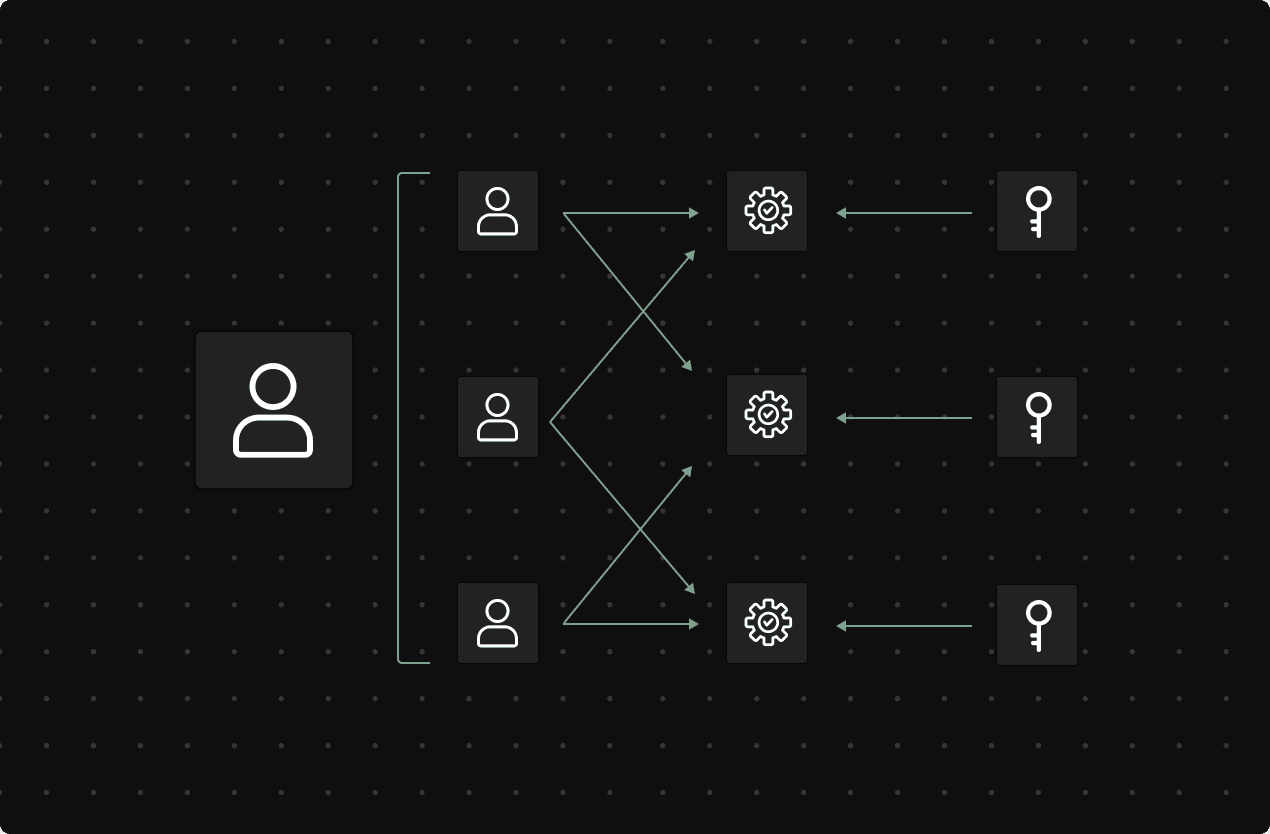
ROLE-BASED ACCESS (RBAC)
Industrial environments require collaboration without overexposure. Role-based access ensures users only interact with the data, systems, and functions relevant to their role.
What this enables:
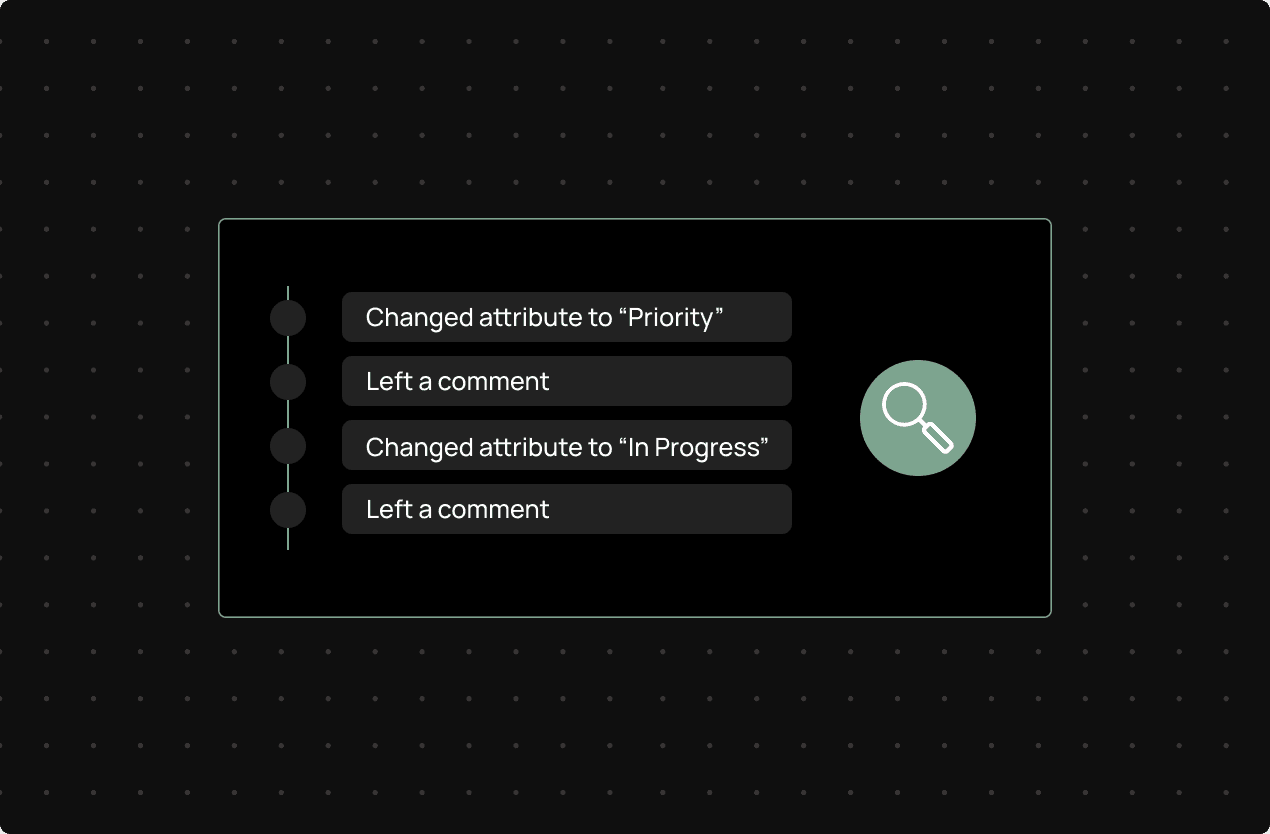
Audit Trails
Security depends on visibility. Audit trails provide traceability across user actions, system changes, and operational events.
What this enables:
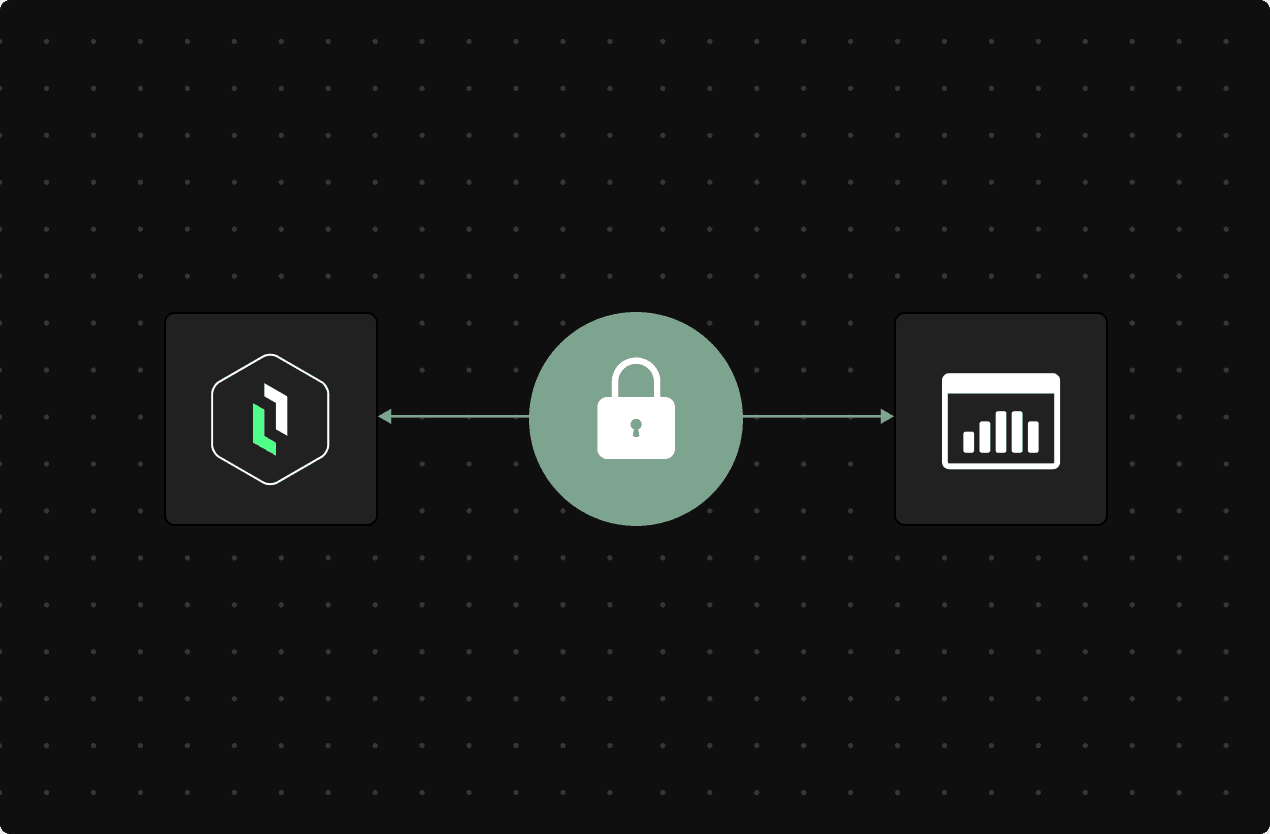
ENCRYPTION & CERTIFICATION
Industrial systems rely on secure communication between devices, services, and platforms. Encryption and certificate management ensure trusted and protected data exchange.
What this enables:
Secure operation across connected, segmented, and isolated environments
Controlled data movement between OT and enterprise systems
Consistent access control across teams and sites
Improved accountability through traceability and auditability
Stronger protection of production systems and workflows
A trusted foundation for analytics, automation, and Industrial AI
Quick answers to your industrial data questions.